The SecOps platform that protects against attacks on the
modern enterprise.
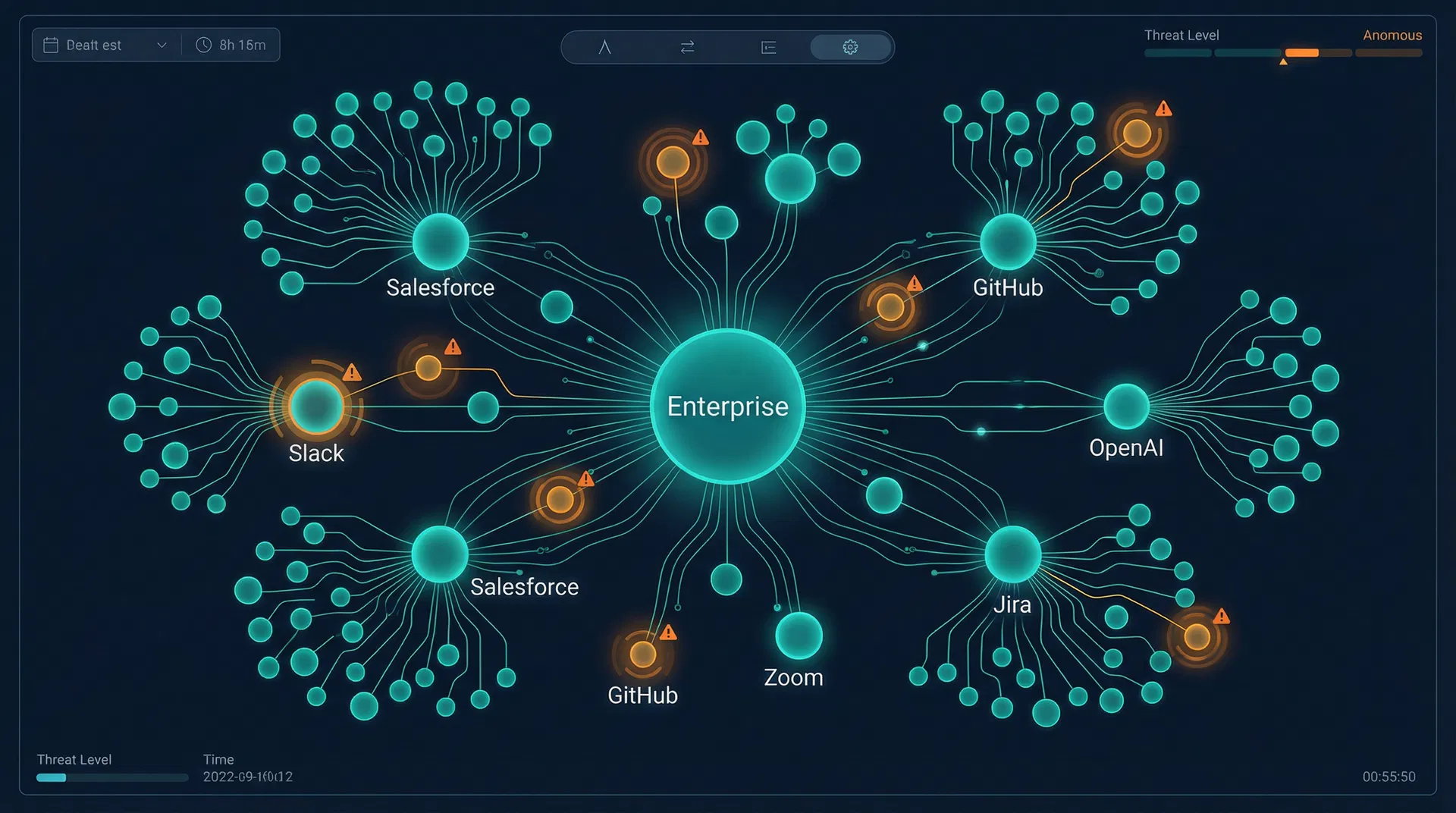
Security still monitors systems. Attacks operate across them. SaaS, APIs, vendors, and AI agents now act with privileged access and growing autonomy. Quake is the detection layer that covers the connections and execution paths between them — where modern attacks actually happen.
SOC Teams Are Blind to
Cross-System Activity
Monitoring access and events is not enough. Enterprises need to start understanding behavior and system intent.
Fragmented Visibility
Activity spans multiple systems, but security teams still investigate them in isolation. There is no unified execution view across connected environments.
No Behavioral Understanding
Trusted activity looks legitimate by default. Without behavioral baselines, drift, misuse, and abuse are hard to distinguish from normal operations.
No Operational Response
When incidents move across systems, blast radius becomes unclear. Investigation is slow, containment is fragmented, and response breaks down.
"Modern attacks increasingly operate through connected workflows, trusted access, integrations, and AI-driven execution. Security today covers endpoints, identities, and cloud — but not third-party integrations, inter-organization connections, or org-to-org workflows."
Hyper-Connected
Detection & Response
HDR is the missing layer in SecOps — Detection & Response for activity operating across hyper-connected environments where SaaS, APIs, vendors, and AI agents act with privileged access and growing autonomy.
Connectors & Ingestion
Connects to SaaS, APIs, AI systems, and proprietary environments to build coverage across the modern enterprise — without requiring a services-heavy model for every new environment.
Context & Correlation
Builds a unified view across systems, identities, data flows, and activity so security teams can understand what is actually happening — not just what access exists.
Behavior & Intent Detection
Learns how connected systems are meant to behave, then detects drift, anomalies, and abuse that appear legitimate in traditional tools. Intent over identity.
Investigation & Containment
Reconstructs execution paths, clarifies blast radius, and enables real operational response across the affected systems — turning fragmented signals into actionable incident response.
| Capability | SSPM | NHI | Quake HDR |
|---|---|---|---|
| Cross-system execution visibility | — | — | ✓ |
| Behavioral baseline per integration | — | — | ✓ |
| Third-party integration monitoring | ✓ | — | ✓ |
| Inter-org connection coverage | — | — | ✓ |
| Intent & drift detection | — | — | ✓ |
| Blast radius analysis | — | — | ✓ |
| SOC-ready operational response | — | — | ✓ |
The Mission Profile
Engine
Every vendor has a job to do. The Mission Profile captures exactly what that job looks like in behavioral terms — creating a multi-dimensional fingerprint that makes anomalies immediately visible.
Passive Learning
Quake monitors vendor behavior for 7–30 days, building a statistical model of normal operations without any configuration required.
Mission Profile Creation
The behavioral baseline is codified into a Mission Profile — a multi-dimensional fingerprint of what 'normal' looks like for this vendor in this environment.
Continuous Drift Detection
Every vendor action is scored against its Mission Profile in real time. Statistical deviations trigger alerts proportional to their severity and context.
Surgical Containment
When drift exceeds thresholds, Quake enables targeted response: throttle the anomalous action, pause the vendor, or block specific API calls — without breaking the integration.
The SOC Transition
Is Happening Now
Every major security category was created in response to a new threat surface. The Integration Era — defined by SaaS sprawl and autonomous AI agents — is creating the next one.
| Era | Years | Primary Tool | Threat Addressed | Remaining Gap |
|---|---|---|---|---|
| Perimeter Era | 1990s–2010 | Firewall / IDS | External attackers trying to get in | Couldn't see inside the network |
| Endpoint Era | 2010–2018 | EDR / AV | Malware on user devices | Couldn't see cloud workloads |
| Cloud Era | 2018–2023 | CDR / CSPM | Misconfigured cloud infrastructure | Couldn't see SaaS vendor behavior |
| Integration Era | 2023–Present | VDR (Quake) | Compromised/rogue vendors & AI agents | This is the gap Quake closes |
Autonomous AI agents
Tools like Devin, Cursor, and Claude Code now execute multi-step workflows autonomously inside enterprise environments — reading codebases, pushing commits, querying databases.
MCP & tool-use protocols
The Model Context Protocol (MCP) enables AI models to call external tools and APIs directly. Every MCP server is a new integration surface with no behavioral monitoring.
Agentic SaaS integrations
Salesforce Agentforce, HubSpot AI, Zendesk AI — every major SaaS vendor is embedding autonomous AI capabilities that act on behalf of users without user-level oversight.
Regulatory pressure
SEC, DORA, and NIS2 are beginning to require demonstrable third-party runtime monitoring. Governance frameworks are catching up to the threat model.
When enterprises moved to cloud, they gained infrastructure they couldn't see. Existing tools (firewalls, EDR) had no visibility into EC2 instances, S3 buckets, or Lambda functions. CDR was created to fill this gap — and became a multi-billion dollar category.
As enterprises adopted SaaS and AI agents, they gained vendors they can't see. Existing tools (SSPM, NHI, SIEM) have no visibility into what vendors are doing at runtime. VDR is being created to fill this gap — and the market timing is identical to CDR in 2018.
Why Existing Tools
Cannot Fill This Gap
Every existing security category was designed for a different threat model. None of them were built to answer the question Quake answers: "Is this vendor behaving normally right now?"
SSPM
Audits SaaS configurations, permissions, and compliance posture. Tells you what access exists.
Configuration-time, not runtime. Cannot detect behavioral anomalies. No containment capability.
Quake operates at runtime, not configuration time. SSPM answers 'what access exists?' — Quake answers 'what is happening right now?'
Vendor-Centric Detection
The fundamental innovation in Quake VDR is the shift from an identity-centric or user-centric detection model to a vendor-centric detection model.
Instead of asking "which user or credential performed this action?" — Quake asks "is this vendor behaving like it normally does?" This reframing creates an entirely new detection surface that existing tools cannot replicate without fundamentally rebuilding their data model.
Why Competitors Cannot
Easily Replicate Quake
Quake's moat is not architectural (inline vs. API-based) — it is perspectival. The vendor-centric lens, the behavioral dataset, and the Mission Profile engine create compounding advantages that incumbents cannot retrofit onto their existing architectures.
The Vendor-First Dataset
Quake accumulates a proprietary dataset of vendor behavioral patterns across thousands of deployments. This dataset — what 'normal' looks like for Salesforce, GitHub, Workday, OpenAI — becomes a compounding moat. Competitors cannot replicate it without years of deployment.
The Mission Profile Engine
The behavioral profiling engine is purpose-built for vendor-centric detection. It understands the difference between a Salesforce CRM integration and a Salesforce Marketing Cloud integration — and profiles each independently. This specificity cannot be retrofitted onto existing identity or log-based architectures.
The Vendor-Centric Threat Model
Quake's detection logic is built around vendor workflows, not user actions or network packets. This means the threat model — what constitutes an anomaly for a CRM vs. a DevOps tool vs. an AI agent — is fundamentally different from any existing SOC tool.
Surgical Containment Architecture
The ability to throttle, pause, or block specific vendor actions (rather than revoking the entire integration) requires deep integration with vendor APIs and a sophisticated action-level control plane. This is a significant engineering investment that incumbents have no incentive to build.
The SOC Workflow Integration
Quake is designed to fit into existing SOC workflows — SIEM ingestion, SOAR playbooks, ticketing integration. This makes it a complement to, not a replacement for, existing tools. This positioning reduces sales friction and accelerates adoption.
First-Mover Advantage in AI Agents
As AI agents proliferate, the need for behavioral monitoring of autonomous systems becomes critical. Quake's Mission Profile engine applies directly to AI agents — creating a first-mover advantage in a market that will be orders of magnitude larger than SaaS vendor monitoring alone.
Perspective is the Moat
CrowdStrike could add vendor monitoring to Falcon. Okta could add behavioral analytics to their NHI product. But they would be building it with a user-centric or identity-centric perspective — and that perspective determines what you can and cannot detect.
Who Needs Quake
VDR Most
The ideal Quake customer has a mature SOC, a complex integration ecosystem, and a CISO who has already been burned by a third-party incident — or is terrified of the next one.
SOC Analyst / IR Lead
Alert fatigue from tools that don't understand vendor context. No way to investigate vendor-specific incidents. Containment requires full token revocation (too disruptive).
Vendor-centric alerts with full behavioral context. Surgical containment that doesn't break integrations. Vendor-specific forensic timelines for IR.
Head of Security Engineering
Growing integration surface with no runtime visibility. AI agent deployments outpacing security controls. No tooling to enforce vendor behavioral policies.
Programmatic vendor behavioral policies. API-first integration with existing security stack. Behavioral baselines that scale automatically.
CISO
Board pressure on third-party risk. Regulatory requirements for vendor runtime monitoring. Cannot demonstrate control over vendor behavior to auditors.
Board-level narrative: 'We monitor vendor behavior at runtime.' Regulatory evidence for DORA, SOC 2, HIPAA. Quantified vendor risk reduction.
Financial Services
Highest regulatory pressure, most mature SOC teams, highest willingness to pay, and most acute vendor sprawl risk (fintech integrations, trading APIs, payment processors).
Enterprise SaaS / AI-Native
Highest AI agent adoption, most complex integration ecosystems, security-conscious engineering culture, and direct understanding of the vendor runtime problem.
HealthTech & Life Sciences
HIPAA and FDA compliance requirements create strong regulatory pull. High-value PHI data makes vendor runtime monitoring a compliance necessity, not just a security best practice.
See what your vendors
are doing right now.
Quake VDR is available for early access to select enterprise SOC teams. If you have 50+ SaaS integrations and a security team that cares about vendor runtime behavior, we want to talk.